
Firewalls made by Zyxel are being wrangled into a destructive botnet, which is taking control of them by exploiting a recently patched vulnerability with a severity rating of 9.8 out of a possible 10.
“At this stage if you have a vulnerable device exposed, assume compromise,” officials from Shadowserver, an organization that monitors Internet threats in real time, warned four days ago. The officials said the exploits are coming from a botnet that’s similar to Mirai, which harnesses the collective bandwidth of thousands of compromised Internet devices to knock sites offline with distributed denial-of-service attacks.
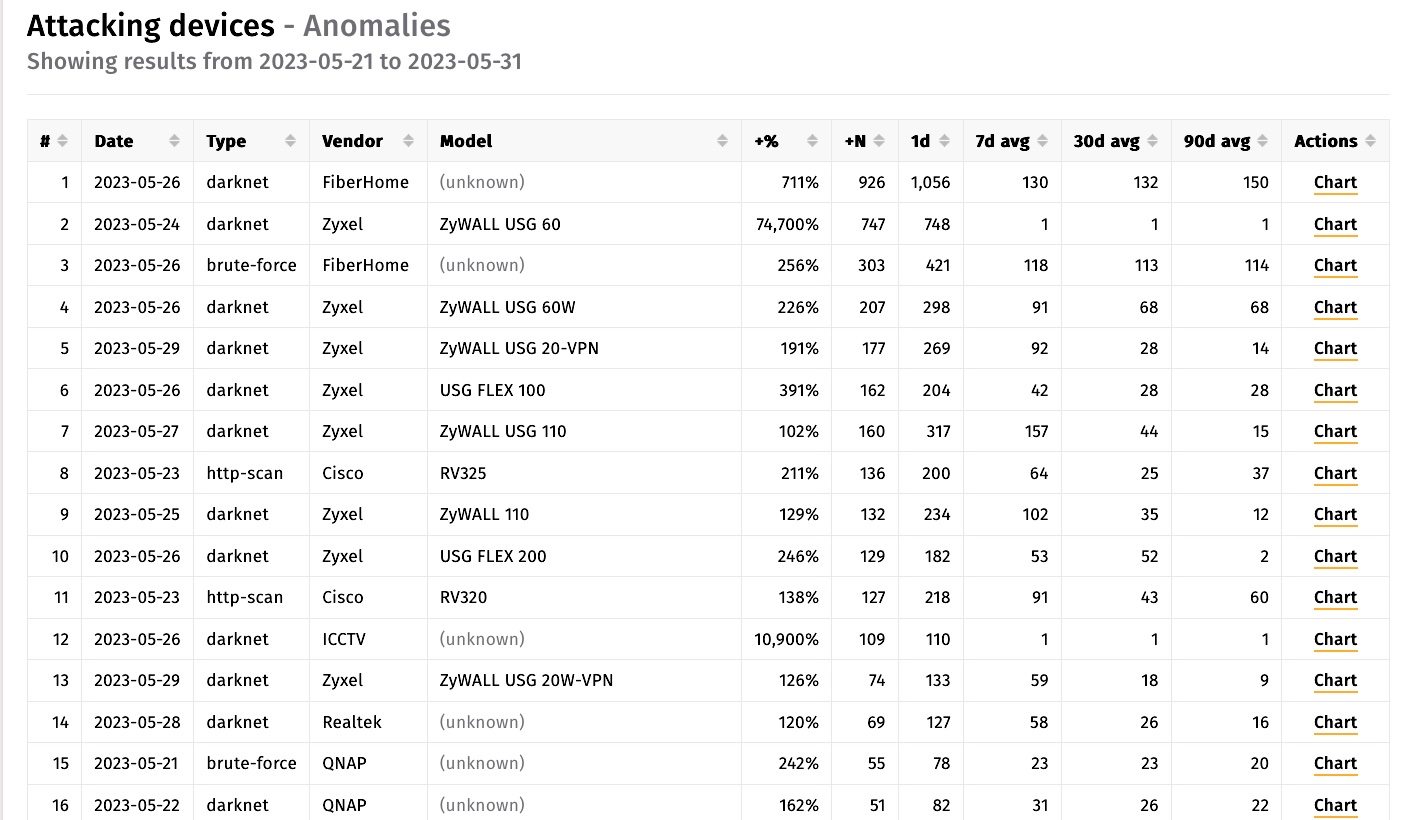
According to data from Shadowserver collected over the past 10 days, 25 of the top 62 Internet-connected devices waging “downstream attacks”—meaning attempting to hack other Internet-connected devices—were made by Zyxel as measured by IP addresses.
A 9.8-severity vulnerability in default configurations
The software bug used to compromise the Zyxel devices is tracked as CVE-2023-28771, an unauthenticated command injection vulnerability with a severity rate of 9.8. The flaw, which Zyxel patched on April 25, can be exploited to execute malicious code with a specially crafted IKEv2 packet to UDP port 500 on the device.
The critical vulnerability exists in default configurations of the manufacturer’s firewall and VPN devices. They include Zyxel ZyWALL/USG series firmware versions 4.60 through 4.73, VPN series firmware versions 4.60 through 5.35, USG FLEX series firmware versions 4.60 through 5.35, and ATP series firmware versions 4.60 through 5.35.
| Affected series | Affected version | Patch availability |
|---|---|---|
| ATP | ZLD V4.60 to V5.35 | ZLD V5.36 |
| USG FLEX | ZLD V4.60 to V5.35 | ZLD V5.36 |
| VPN | ZLD V4.60 to V5.35 | ZLD V5.36 |
| ZyWALL/USG | ZLD V4.60 to V4.73 | ZLD V4.73 Patch 1 |
On Wednesday, the Cybersecurity and Infrastructure Security Agency placed CVE-2023-28771 on its list of known exploited vulnerabilities. The agency has given federal agencies until June 21 to fix any vulnerable devices in their networks.
Security researcher Kevin Beaumont has also been warning of widespread exploitation of the vulnerability since last week.
“This #Zyxel vuln is being mass exploited now by Mirai botnet,” he wrote on Mastodon. “A fuck ton of SMB VPN boxes are owned.”
Measurements from the Shodan search engine show almost 43,000 instances of Zyxel devices exposed to the Internet.
“This number only includes devices that expose their web interfaces on the WAN, which is not a default setting,” Rapid7 said, using the abbreviation for wide area network, the part of a company’s network that can be accessed over the Internet. “Since the vulnerability is in the VPN service, which is enabled by default on the WAN, we expect the actual number of exposed and vulnerable devices to be much higher.”
A VPN—short for virtual private network—doesn’t need to be configured on a device for it to be vulnerable, Rapid7 said. Zyxel devices have long been a favorite for hacking because they reside at the edge of a network, where defenses are typically lower. Once infected, attackers use the devices as a launch pad for compromising other devices on the Internet or as a toe-hold that can be used to spread to other parts of the network they belong to.
While most of the focus is on CVE-2023-28771, Rapid7 warned of two other vulnerabilities—CVE-2023-33009 and CVE-2023-33010 — that Zyxel patched last week. Both vulnerabilities also carry a 9.8 severity rating.
With infections from CVE-2023-28771 still occurring five weeks after Zyxel fixed it, it’s clear many device owners aren’t installing security updates in a timely manner. If the poor patching hygiene carries over to the more recently fixed vulnerabilities, there likely will be more Zyxel compromises occurring soon.
