
Microsoft researchers have discovered a hybrid Windows-Linux botnet that uses a highly efficient technique to take down Minecraft servers and performs distributed denial-of-service attacks on other platforms.
Dubbed MCCrash, the botnet infects Windows machines and devices running various distributions of Linux for use in DDoS attacks. Among the commands the botnet software accepts is one called ATTACK_MCCRASH. This command populates the user name in a Minecraft server login page with ${env:random payload of specific size:-a}. The string exhausts the resources of the server and makes it crash.
“The usage of the env variable triggers the use of Log4j 2 library, which causes abnormal consumption of system resources (not related to Log4Shell vulnerability), demonstrating a specific and highly efficient DDoS method,” Microsoft researchers wrote. “A wide range of Minecraft server versions can be affected.”
Currently, MCCrash is hardcoded to target only version 1.12.2 of the Minecraft server software. The attack technique, however, will take down servers running versions 1.7.2 through 1.18.2, which run about half of the world’s Minecraft servers. If the malware is updated to target all vulnerable versions, its reach could be much wider. A modification in Minecraft server version 1.19 prevents the attack from working.
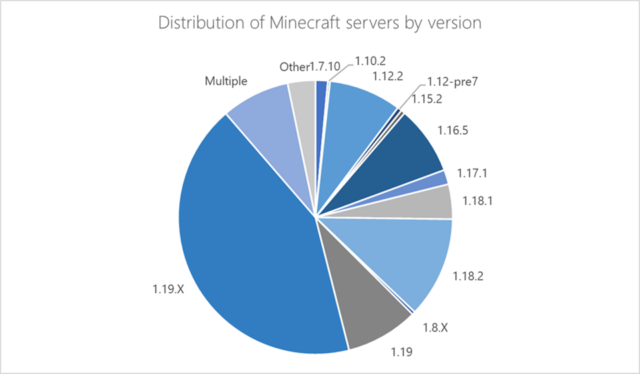
“The wide range of at-risk Minecraft servers highlights the impact this malware could have had if it was specifically coded to affect versions beyond 1.12.2,” Microsoft researchers wrote. “The unique ability of this threat to utilize IoT devices that are often not monitored as part of the botnet substantially increases its impact and reduces its chances of being detected.”
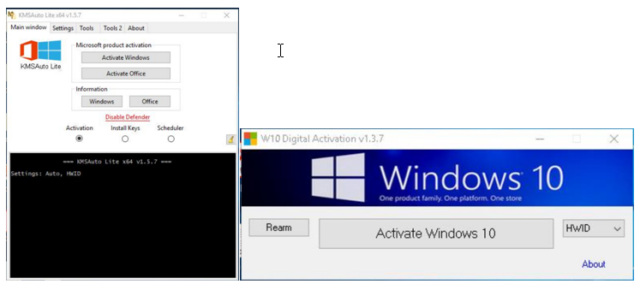
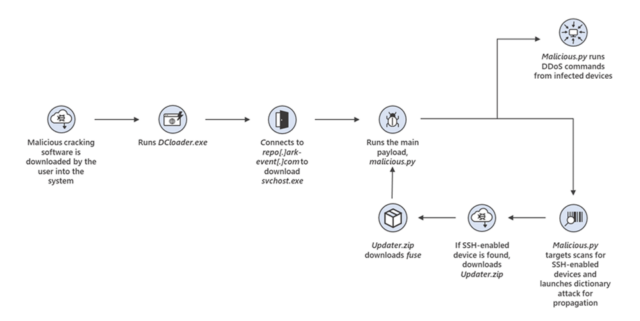
The initial infection point for MCCrash is Windows machines that have installed software that purports to give pirated licenses for the Microsoft OS. Code hidden in the downloaded software surreptitiously infects the device with malware that eventually installs malicious.py, a python script that provides the main logic for the botnet. Infected Windows devices then scan the Internet in search of Debian, Ubuntu, CentOS, and IoT devices that accept SSH connections.
When found, MCCrash uses common default login credentials in an attempt to run the same malicious.py script on the Linux device. Both the Windows and Linux devices are then part of a botnet that performs the Minecraft attack as well as other forms of DDoSes. The graphic below shows the attack flow.
A breakdown of devices infected by MCCrash shows that most of them are located in Russia. Microsoft didn’t say how many devices are infected. Company researchers said they believe the botnet operators use it to sell DDoS services on crime forums.
