
Android apps with hundreds of millions of downloads are vulnerable to attacks that allow malicious apps to steal contacts, login credentials, private messages, and other sensitive information. Security firm Check Point said that the Edge Browser, the XRecorder video and screen recorder, and the PowerDirector video editor are among those affected.
The vulnerability actually resides in the Google Play Core Library, which is a collection of code made by Google. The library allows apps to streamline the update process by, for instance, receiving new versions during runtime and tailoring updates to an individual app’s specific configuration or a specific phone model the app is running on.
A core vulnerability
In August, security firm Oversecured disclosed a security bug in the Google Play Core Library that allowed one installed app to execute code in the context of any other app that relied on the vulnerable library version.
The vulnerability stemmed from a directory traversal flaw that allowed untrusted sources to copy files to a folder that was supposed to be reserved only for trusted code received from Google Play. The vulnerability undermined a core protection built into the Android operating system that prevents one app from accessing data or code belonging to any other app.
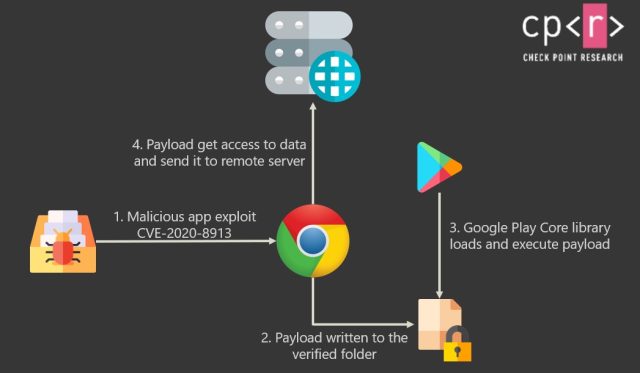
Here’s an image that illustrates how an attack might work:
Google patched the library bug in April, but for vulnerable apps to be fixed, developers must first download the updated library and then incorporate it into their app code. According to research findings from Check Point, a nontrivial number of developers continued to use the vulnerable library version.
Check Point researchers Aviran Hazum and Jonathan Shimonovich wrote:
When we combine popular applications that utilize the Google Play Core library, and the Local-Code-Execution vulnerability, we can clearly see the risks. If a malicious application exploits this vulnerability, it can gain code execution inside popular applications and have the same access as the vulnerable application.
The possibilities are limited only by our creativity. Here are just a few examples:
- Inject code into banking applications to grab credentials, and at the same time have SMS permissions to steal the Two-Factor Authentication (2FA) codes.
- Inject code into Enterprise applications to gain access to corporate resources.
- Inject code into social media applications to spy on the victim, and use location access to track the device.
- Inject code into IM apps to grab all messages, and possibly send messages on the victim’s behalf.
Seeing is believing
To demonstrate an exploit, Check Point used a proof-of-concept malicious app to steal an authentication cookie from an old version of Chrome. With possession of the cookie, the attacker is then able to gain unauthorized access to a victim’s Dropbox account.
Check Point identified 14 apps with combined downloads of almost 850 million that remained vulnerable. Within a few hours of publishing a report, the security firm said that developers of some of the named apps had released updates that fixed the vulnerability.
Apps identified by Check Point included Edge, XRecorder, and the PowerDirector, which have combined installations of 160 million. Check Point provided no indication that any of these apps had been fixed. Ars asked developers of all three apps to comment on the report. This post will be updated if they respond.
