The Microsoft Exchange vulnerabilities that allow hackers to take over Microsoft Exchange servers are under attack by no fewer than 10 advanced hacking groups, six of which began exploiting them before Microsoft released a patch, researchers reported Wednesday. That raises a vexing question: how did so many separate threat actors have working exploits before the security flaws became publicly known?
Researchers say that as many as 100,000 mail servers around the world have been compromised, with those for the European Banking Authority and Norwegian Parliament being disclosed in the past few days. Once attackers gain the ability to execute code on the servers, they install web shells, which are browser-based windows that provide a means for remotely issuing commands and executing code.
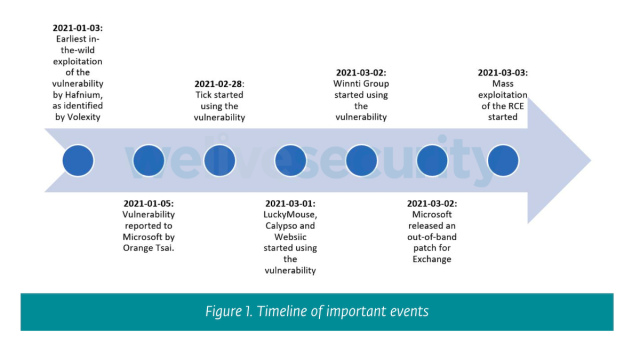
When Microsoft issued emergency patches on March 2, the company said the vulnerabilities were being exploited in limited and targeted attacks by a state-backed hacking group in China known as Hafnium. On Wednesday, ESET provided a starkly different assessment. Of the 10 groups ESET products have recorded exploiting vulnerable servers, six of those APTs—short for advanced persistent threat actors—began hijacking servers while the critical vulnerabilities were still unknown to Microsoft.
It’s not often that a so-called zero-day vulnerability is exploited by two groups in unison, but it happens. A zero-day under attack by six APTs simultaneously, on the other hand, is highly unusual, if not unprecedented.
“Our ongoing research shows that not only Hafnium has been using the recent RCE vulnerability in Exchange, but that multiple APTs have access to the exploit, and some even did so prior to the patch release,” ESET researchers Matthieu Faou, Mathieu Tartare, and Thomas Dupuy wrote in a Wednesday post. “It is still unclear how the distribution of the exploit happened, but it is inevitable that more and more threat actors, including ransomware operators, will have access to it sooner or later.”
Beyond unlikely
The mystery is compounded by this: within a day of Microsoft issuing the patches, at least three more APTs joined the fray. A day later, another one was added to the mix. While it’s possible that those four groups reverse-engineered the fixes, developed weaponized exploits, and deployed them at scale, those types of activities usually take time. A 24-hour window is on the short side.
There’s no clear explanation for the mass exploitation by so many different groups, leaving researchers few alternatives other than to speculate.
“It would seem that while the exploits were originally used by Hafnium, something made them share the exploit with other groups around the time the associated vulnerabilities were getting patched by Microsoft,” Costin Raiu, director of the Global Research and Analysis Team at Kaspersky Lab, told me. “This could suggest a certain degree of cooperation between these groups, or it may also suggest the exploits were available for sale in certain markets and the potential of them getting patched resulted in a drop of price, allowing others to acquire it as well.”
Juan Andres Guerrero-Saade, principal threat researcher at security firm SentinelOne, arrived at largely the same assessment.
“The idea that six groups coming from the same region would independently discover the same chain of vulnerabilities and develop the same exploit is beyond unlikely,” he wrote in a direct message. “The simpler explanation is that there’s (a) an exploit seller in common, (b) an unknown source (like a forum) available to all of these, or (c) a common entity that organizes these different hacking groups and provided them the exploit to ease their activities (say, China’s Ministry of State Security).”
Naming names
The six groups ESET identified exploiting the vulnerabilities when they were still zero-days are:
- Hafnium: The group, which Microsoft said is state sponsored and based in China, was exploiting the vulnerabilities by early January.
- Tick (also known as Bronze Butler and RedBaldKnight): On February 28, two days before Microsoft issued patches, this group used the vulnerabilities to compromise the web server of an East Asian IT services company. Tick has been active since 2018 and targets organizations mostly in Japan but also in South Korea, Russia, and Singapore.
- LuckyMouse (APT27 and Emissary Panda): On March 1, this cyber-espionage group known to have breached multiple government networks in Central Asia and the Middle East compromised the email server of a governmental entity in the Middle East.
- Calypso (with ties to Xpath): On March 1, this group compromised the email servers of governmental entities in the Middle East and South America. In the following days, it went on to target organizations in Africa, Asia, and Europe. Calypso targets governmental organizations in these regions.
- Websiic: On March 1, this APT, which ESET had never seen before, targeted mail servers belonging to seven Asian companies in the IT, telecommunications, and engineering sectors and one governmental body in Eastern Europe.
- Winnti (aka APT 41 and Barium): Just hours before Microsoft released the emergency patches on March 2, ESET data shows this group compromising the email servers of an oil company and a construction equipment company, both based in East Asia.
ESET said it saw four other groups exploiting the vulnerabilities in the days immediately following Microsoft’s release of the patch on March 2. Two unknown groups started the day after. Two other groups, known as Tonto and Mikroceen, began on March 3 and March 4, respectively.
China and beyond
Joe Slowik, senior security researcher at security firm DomainTools, published his own analysis on Wednesday and noted that three of the APTs that ESET saw exploiting the vulnerabilities ahead of the patches—Tick, Calypso, and Winnti—have previously been linked to hacking sponsored by the People’s Republic of China. Two other APTs that ESET saw exploiting the vulnerabilities a day after the patches—Tonto and Mikroceen—also have ties to the PRC, the researcher said.
Slowik produced the following timeline:
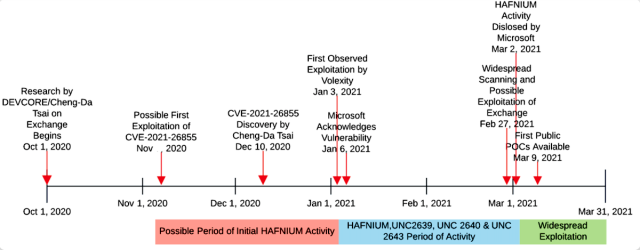
The timeline includes three exploitation clusters that security firm FireEye has said were exploiting the Exchange vulnerabilities since January. FireEye referred to the groups as UNC2639, UNC2640, and UNC2643 and didn’t tie the clusters to any known APTs or say where they were located.
Because different security firms use different names for the same threat actors, it’s not clear if the groups identified by FireEye overlap with those seen by ESET. If they were distinct, the number of threat actors exploiting the Exchange vulnerabilities prior to a patch would be even higher.
A range of organizations under siege
The tracking of the APTs came as the FBI and the Cybersecurity and Infrastructure Security Agency issued an advisory on Wednesday that said threat groups are exploiting organizations including local governments, academic institutions, non-governmental organizations, and business entities in a range of industries, including agriculture, biotechnology, aerospace, defense, legal services, power utilities, and pharmaceutical.
“This targeting is consistent with previous targeting activity by Chinese cyber actors,” the advisory stated. With security firm Palo Alto Networks reporting on Tuesday that an estimated 125,000 Exchange servers worldwide were vulnerable, CISA and FBI officials’ call for organizations to patch took on an extra measure of urgency.
Both ESET and security firm Red Canary have seen exploited Exchange servers that were infected with DLTMiner, a piece of malware that allows attackers to mine cryptocurrency using the computing power and electricity of infected machines. ESET, however, said it wasn’t clear if the actors behind those infections had actually exploited the vulnerabilities or had simply taken over servers that had already been hacked by someone else.
With so many of the pre-patch exploits coming from groups tied to the Chinese government, the hypothesis from SentinalOne’s Guerrero-Saade—that a PRC entity provided the exploits to multiple hacking groups ahead of the patches—seems to be the simplest explanation. That theory is further supported by two other PRC-related groups—Tonto and Mikroceen—being among the first to exploit the vulnerabilities following Microsoft’s emergency release.
Of course, it’s possible that the half-dozen APTs that exploited the vulnerabilities while they were still zero-days independently discovered the vulnerabilities and developed weaponized exploits. If that’s the case, it’s likely a first, and hopefully a last.
