As many as 1,500 businesses around the world have been infected by highly destructive malware that first struck software maker Kaseya. In one of the worst ransom attacks ever, the malware, in turn, used that access to fell Kaseya’s customers.
The attack struck on Friday afternoon in the lead-up to the three-day Independence Day holiday weekend in the US. Hackers affiliated with REvil, one of ransomware’s most cutthroat gangs, exploited a zero-day vulnerability in the Kaseya VSA remote management service, which the company says is used by 35,000 customers. The REvil affiliates then used their control of Kaseya’s infrastructure to push a malicious software update to customers, who are primarily small-to-midsize businesses.
Continued escalation
In a statement posted on Monday, Kaseya said that roughly 50 of its customers were compromised. From there, the company said, 800 to 1,500 businesses that are managed by Kaseya’s customers were infected. REvil’s site on the dark web claimed that more than 1 million targets were infected in the attack and that the group was demanding $70 million for a universal decryptor.
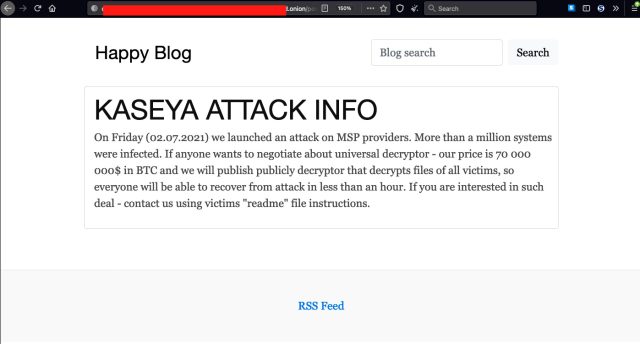
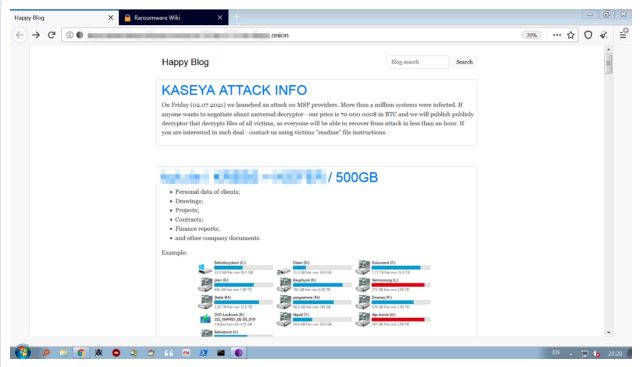
REvil’s site had been updated to remove an image purportedly showing hard drives with 500GB of data locked up. Ransomware groups often remove information from their sites once ransom negotiations begin as a sign of good faith. Here’s how the image looked previously:
“It is not a great sign that a ransomware gang has a zero day in a product used widely by Managed Service Providers, and shows the continued escalation of ransomware gangs—which I’ve written about before,” security expert and independent researcher Kevin Beaumont wrote.
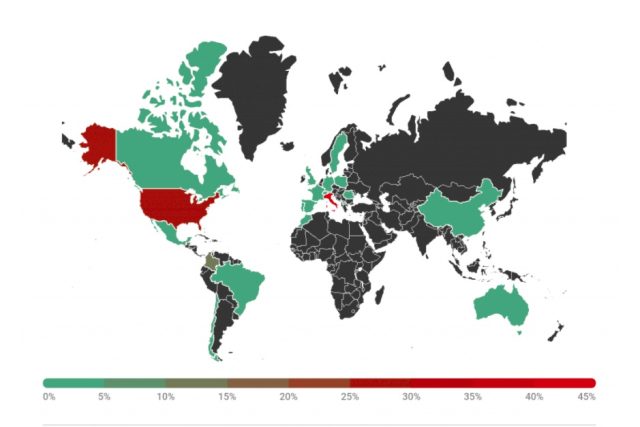
The mass attack had cascading effects around the world. Swedish supermarket chain Coop on Tuesday was still trying to recover after it shut about half of its 800 stores because point-of-sale tills and self-service checkouts stopped working. Schools and kindergartens in New Zealand were also affected, as were some public administration offices in Romania. Germany’s cybersecurity watchdog, BSI, said on Tuesday that it was aware of three IT service providers in Germany that have been affected. The map below shows where security firm Kaspersky is seeing infections.
REvil has earned a reputation as a ruthless and sophisticated group, even in notoriously brazen ransomware circles. Its most recent big-game victim was meatpacking giant JBS, which in June shut down a huge swath of its international operations after the ransomware hamstrung its automated processes. JBS ultimately paid REvil affiliates $11 million.
REvil’s previous victims include Taiwanese multinational electronics corporation Acer in March as well as attempt in April to extort Apple following an attack against one of its business partners. REvil is also the group that hacked Grubman Shire Meiselas & Sacks, the celebrity law firm that represented Lady Gaga, Madonna, U2, and other top-flight entertainers. When REvil demanded $21 million in return for not publishing the data, the law firm reportedly offered $365,000. REvil responded by upping its demand to $42 million and later publishing a 2.4GB archive containing some Lady Gaga legal documents.
Still other REvil victims include Kenneth Copeland, SoftwareOne, Quest, and Travelex.
Surgical precision
This weekend’s attack was carried out with almost surgical precision. According to Cybereason, the REvil affiliates first gained access to targeted environments and then used the zero-day in the Kaseya Agent Monitor to gain administrative control over the target’s network. After writing a base-64-encoded payload to a file named agent.crt the dropper executed it.
Here’s the flow of the attack:
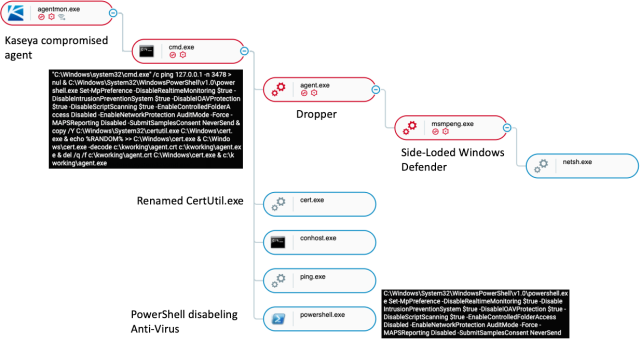
The ransomware dropper Agent.exe is signed with a Windows-trusted certificate that uses the registrant name “PB03 TRANSPORT LTD.” By digitally signing their malware, attackers are able to suppress many security warnings that would otherwise appear when it’s being installed. Cybereason said that the certificate appears to have been used exclusively by REvil malware that was deployed during this attack.
To add stealth, the attackers used a technique called DLL Side-Loading, which places a spoofed malicious DLL file in a Windows’ WinSxS directory so that the operating system loads the spoof instead of the legitimate file. In the case here, Agent.exe drops an outdated version that is vulnerable to DLL Side-Loading of “msmpeng.exe,” which is the file for the Windows Defender executable.
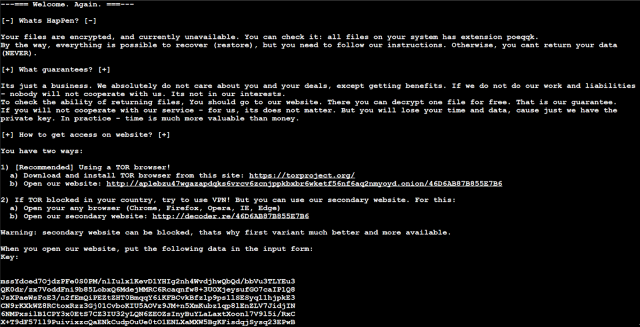
Once executed, the malware changes the firewall settings to allow local windows systems to be discovered. Then, it starts to encrypt the files on the system and displays the following ransom note:
Kaseya has said that all attacks it has discovered to date targeted its on-premises product.
“All on-premises VSA Servers should continue to remain offline until further instructions from Kaseya about when it is safe to restore operations,” the company said in an advisory. “A patch will be required to be installed prior to restarting the VSA and a set of recommendations on how to increase your security posture.”
The company said it has found evidence that any of its cloud customers were compromised.
The REvil affiliates exploited a zeroday vulnerability that Kaseya was days away from patching when the attack hit. CVE-2021-30116, as the vulnerability was tracked, was discovered by researchers from the Dutch Institute for Vulnerability Disclosure, which says its researchers had privately reported the security flaw and was monitoring Kaseya’s progress in patching it.
Kaseya “showed a genuine commitment to do the right thing,” representatives of the institute wrote. “Unfortunately, we were beaten by REvil in the final sprint, as they could exploit the vulnerabilities before customers could even patch.”
The event is the latest example of a supply chain attack, in which hackers infect the provider of a widely used product or service with the goal of compromising downstream customers who use it. In this case, the hackers infected Kaseya customers and then used that access to infect the businesses that received service from Kaseya.
The SolarWinds compromise discovered in December was another such supply-chain attack. It used SolarWinds hacked software build infrastructure to push a malicious software update to 18,000 organizations that used the company’s network management tool. About nine federal agencies and 100 private organizations received follow-on infections.
Anyone who suspects their network has been affected in any way in this attack should investigate immediately. Kaseya has published a tool that VSA customers can use to detect infections in their networks. The FBI and the Cybersecurity and Infrastructure Security Agency have jointly issued recommendations for Kaseya customers, particularly if they’ve been compromised.
